‘Geofence’ Warrants Threaten Every Phone User’s Privacy
The last time your phone asked you to allow this or that app access to your location data, you may have had some trepidation about how much Apple or Google know about you. You may have worried about what might come of that, or read about China’s use of the data to track anti-lockdown protesters. What you probably didn’t realize is Google has already searched your data on behalf of the federal government to see if you were involved with January 6th.
But last month, the federal district court in DC issued an opinion in the case of one of the many defendants who stands accused of sacking the Capitol in the wake of the 2020 election.
And with it, Judge Rudolph Contreras became the first federal district judge to approve a “Geofence” warrant, endorsing a recent police innovation: searching the cell phone history of every American to check who happened to be in the area of some potential crime.
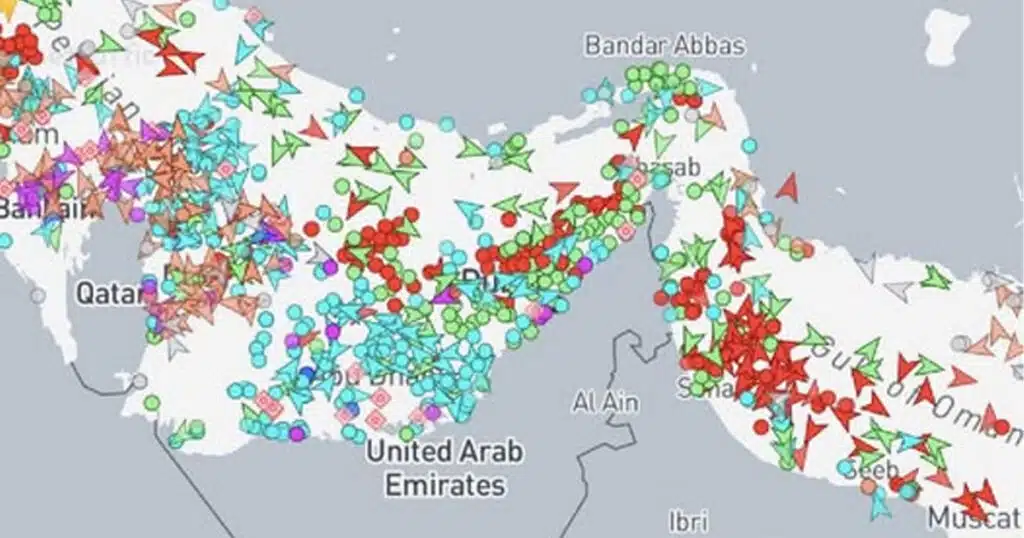
The “Geofence” in this context refers to cell phone location data collected by Google from users of its Android operating system, as well as iPhone users who use apps such as Google Maps. Location tracking can be turned off, but most users allow it for the convenience of getting directions, tracking their daily jog, or finding the nearest Chipotle. The Government’s warrant demanded location history for every Google account holder within a range of longitude and latitude roughly corresponding to the Capitol building on the afternoon of January 6, 2021, along with similar data from that morning and evening (to filter out Hill staff and security guards).
It’s not clear this information was even needed: This defendant was apprehended within the building that day, carrying knives and pepper spray, and features on various security cameras — his whereabouts are not in question. Many of his coreligionists were considerate enough to live stream their antics themselves. While tracking down every participant in what was dubbed the Beer Belly Putsch is impractical, prosecutors have not lacked for defendants, or for evidence against them. But the government nonetheless decided to resort to a level of mass surveillance without precedent in history or criminal law. This is only the second federal district judge to rule on such a warrant, and the first, in the Eastern District of Virginia, found it “invalid for lack of particularized probable cause” (though that judge declined to suppress the evidence on the basis of other Fourth Amendment loopholes created by the Supreme Court).
That particular requirement comes from the Fourth Amendment itself, which calls for every warrant to “particularly describ[e] the place to be searched, and the persons or things to be seized.” This means that, for instance, the warrant issued last year for former President Trump’s Florida residence did not simply say “search the house,” but detailed specific rooms to be searched for specific things (boxes of documents). The cops can’t — or at least are not supposed to — dump out your underwear drawer based on a tip that you’re hiding cocaine in your basement.
It’s difficult to imagine how a Geofence warrant could ever be particularized in the sense the Fourth Amendment is supposed to require. Traditionally, the government would identify a list of suspects, and then ask the phone company for records specific to them. Geofencing reverses the order of operations: Now the government demands the data of everyone, and only decides which of us is guilty or innocent after invading the privacy of both. In order to find the phones within the Geofence, Google must search their entire repository — if you have a google account, you were searched alongside the perpetrators. It’s difficult to distinguish this approach from the practice that inspired the Fourth Amendment in the first place: the English “general warrants,” which allowed customs officers broad latitude to search any home they liked for smuggled goods.
One might cut Judge Contreras some slack on the basis that the existing Fourth Amendment law he is obliged to apply comes from the era of pay phones and radio transmitters. Traditional doctrine turns on a citizen’s “expectation of privacy,” and holds that there is little such expectation in one’s public movements. This struck a perhaps reasonable balance between privacy and the needs of law enforcement in an era where, if the police wanted to track you, they had to dedicate scarce manpower to maintaining a tail — resource constraints typically restricted surveillance to those reasonably under suspicion.
Over the past decade, the Supreme Court has attempted to grapple with how to apply these principles to modern technology. In Riley v. California, the Court held that unlike pockets and purses, the police cannot automatically search the smartphone of anyone they arrest. The opinion turned on the sheer breadth of material available on our personal devices: one might keep a bit of personal information in one’s purse or wallet, but nothing like what’s a few clicks away on any iPhone: texts, emails, calendars, intimate photos, bank accounts, how many calories the owner has eaten that day and which friends they’ve paid money to in recent weeks for which reasons. The Court held that this new reality required new rules for law enforcement.
A few years later, in Carpenter v. United States, the Supreme Court addressed the use of Cell Site Location Information, the phone company’s record of which cell towers you phone connects to. This data provides a rough approximation of your whereabouts, but without the precision of Google’s location data — a given cell tower narrows your location down to a couple blocks, whereas Google’s estimated margin of error averages closer to 100 meters. The Supreme Court said that Cell Site data requires a warrant, a break from existing law which held one could not expect privacy in one’s public whereabouts. And the cops in Carpenter had identified a specific phone belonging to their suspect and match its locations to a string of robberies — they hadn’t asked Verizon to track every phone in Michigan and Ohio.
One need not have sympathy for the QAnon shamans and oath-breakers to judge that this sort of digital dragnet empowers law enforcement in new and often frightening ways. The Fourth Amendment protects the rights of the accused in criminal prosecutions, and denying those protections to the guilty will ultimately harm the innocent. Police could demand location data for every phone brought to a BlackLivesMatter rally, or an NRA convention; they could identify every woman who visits an abortion clinic, or attends the March for Life.
Federal criminal law has metastasized to the point where the average person probably commits multiple federal crimes on the average day — which of us is prosecuted depends mostly on the priorities and caprice of law enforcement. If you want a vision of the future, imagine your phone ratting you out to the cops, forever.
Reilly Stephens is a Staff Attorney at Liberty Justice Center.
This article was originally published by RealClearPolicy and made available via RealClearWire.